Cyber-Enabled Cargo Theft in 2026: How AI-Powered Criminals Are Targeting Your Freight
Mar 12, 2026
Scroll to explore

TLDR
Stolen shipment losses surged 60% to ~$725M in 2025. Digital intrusion now precedes and enables physical theft of goods across the transportation industry. Criminals use AI, phishing, and deepfake voice calls to compromise dispatch systems and hijack loads before anyone detects the breach. Every broker handoff is an unverified access point. Fewer intermediaries mean a smaller attack surface for your supply chain. Direct, verified carrier connections backed by five-layer compliance break the attack chain at step one. |
Cargo theft used to mean cut padlocks and hijacked trucks. The National Motor Freight Traffic Association’s 2026 transportation industry cybersecurity trends report tells a different story: digital intrusion now routinely precedes the physical theft of shipments. Criminals aren’t breaking into trailers — they’re compromising your logistics partners’ systems weeks before a single load disappears.
For supply chain analysts, this shifts the risk equation. Your fleet’s posture is only as strong as the weakest link in your network — and every intermediary handoff is a vulnerability that organized criminals exploit at scale.
How Criminals Exploit Broker and Carrier Vulnerabilities Through Social Engineering and AI
Today’s cargo thieves don’t need to touch your truck to steal what’s inside. They need access to one compromised system in the intermediary chain. Per SecurityWeek, organized syndicates blend hacker tactics with social engineering in coordinated campaigns targeting logistics companies, carriers, and shippers simultaneously.
The attack chain is repeatable. A phishing email gives the criminal initial access to a motor carrier’s dispatch systems or load board credentials. Thieves then impersonate legitimate carriers, spoof GPS signals, and hijack shipments using fraudulent bills of lading — before anyone in the transportation sector detects the intrusion.
AI accelerates every stage. Deepfake voice calls replicate dispatcher voices. AI-driven reconnaissance scans continuously for exposed systems. Phishing generated by machine learning bypasses traditional detection. For shippers, the structural lesson is clear: every intermediary between you and the truck hauling your goods is a vulnerability. Traditional methods required proximity. Cyber-enabled cargo theft requires only a laptop.
What the NMFTA 2026 Cybersecurity Trends Report Reveals About Fleet and Freight Risk
The NMFTA’s report — the most comprehensive assessment of transportation cybersecurity in 2026 — documents a sector where digital compromise and the physical loss of shipments are operationally inseparable.
Metric | 2025 Finding |
Estimated losses from stolen shipments | ~$725M (up 60%) |
Confirmed incidents | 2,646 (up 18%) |
Average stolen shipment value | $273,990 (up 36%) |
Q3 2025 claims alone | $111.88M |
Average attacker breakout time | 18 minutes |
Ransomware attacks on transportation | Doubled YoY |
Sources: Verisk CargoNet, NMFTA 2026 Report, National Insurance Crime Bureau
Ransomware and extortion groups now steal sensitive fleet and operational data before threatening to publish it. An 18-minute breakout time means attackers move laterally through a network before manual detection and response can engage. Fleets investing in cybersecurity awareness training saw measurable reductions in social engineering attacks, per the National Motor Freight Traffic Association. But cyber maturity varies dramatically — and shippers bear the cost when their partners fall behind.
Why Resilience Starts with Fewer Handoffs: Securing Your Supply Chain Through Direct Connections
Most guidance on trucking cybersecurity focuses on fleet-side defenses: MFA, network segmentation, awareness training. Necessary — but it misses the shipper’s core question: how do you protect goods when the vulnerability exists inside someone else’s operation?
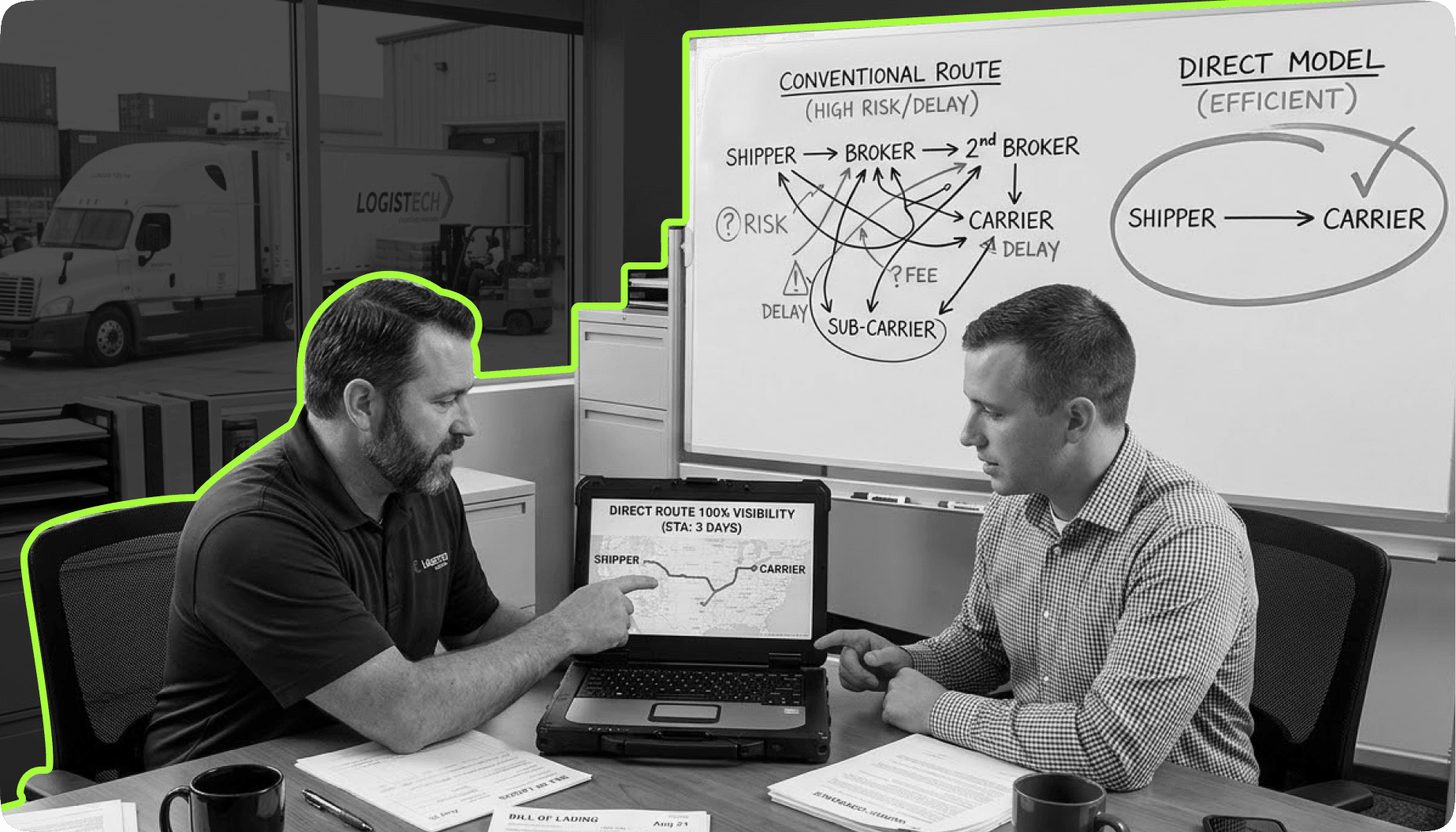
The answer is structural. Every broker in a supply chain adds an access point criminals can compromise. Direct shipper-to-carrier connections backed by continuous five-layer compliance (DOT, insurance, safety, fraud detection, live tracking) collapse the attack surface. HaulerHub’s trust infrastructure delivers this: verified connections with vetted partners that close the intermediary gaps hackers depend on.
Robust security requires fewer handoffs, continuous validation, and proven prevention strategies that address identity fraud at the source. When a shipper connects directly with a verified partner through a platform that monitors cyber hygiene and compliance in real time, the attack chain breaks at step one. NMFTA is driving industry-wide improvement through collaboration and standards. For individual shippers, the highest-impact move is eliminating the structural gap: the fragmented intermediary model itself.
Key Takeaways
Digital intrusion enables physical loss of freight. The NMFTA’s 2026 report makes the link unmistakable. AI accelerates both sides — but without verified connections, defensive tools patch a fundamentally leaky system. Every intermediary is an access point. Fewer handoffs mean a smaller attack surface. Direct connections backed by five-layer compliance eliminate the structural gaps criminals depend on. Cybersecurity must become a selection criterion when choosing logistics partners — not just an internal IT initiative. |
Stop Trusting the Chain. Start Verifying It. HaulerHub’s five-layer compliance eliminates the intermediary gaps that criminals depend on. |
FAQ
FAQ: Cyber-Enabled Freight Crime and Trucking Cybersecurity in 2026
Q1. What is cyber-enabled cargo theft?
The use of digital tactics — phishing, credential compromise, GPS spoofing, and AI-powered social engineering — to facilitate physical theft of goods. Unlike traditional methods relying on force, this approach starts with system compromise weeks before a load vanishes.
Q2. How does AI make these attacks worse in 2026?
AI automates reconnaissance, generates convincing phishing at scale, and powers deepfake impersonation of dispatchers across the logistics and transportation sector.
Q3. What can shippers do to protect their operations?
Reduce intermediaries in your network, verify compliance continuously rather than at onboarding, and connect directly with partners that meet robust cybersecurity standards. Platforms like HaulerHub close the gaps these criminals exploit.
Q4. What did the NMFTA 2026 report find about fleet risk?
Digital compromise now routinely precedes physical loss of shipments. Theft and fleet risk are inseparable from trucking cybersecurity: ransomware doubled, breakout times hit 18 minutes, and AI-assisted fraud became nearly undetectable.
Checkout other blogs

Stay ahead of the supply chain.
Break free from costly and complex systems. Sign up with HaulerHub now and make shipping a breeze.



